AI start-ups in the field of security solutions
Artificial intelligence and machine learning can be excellent assistants to staff shortages of security teams who need to respond faster and more effectively to cyber threats.
It has long become clear that companies must respond to an ever-increasing number of security alerts. And given the speed with which in 2017, extortion virus attacks spread throughout the world, and the increasingly stringent legal requirements, the response should be much faster. In the face of a shortage of relevant specialists, companies turn to machine learning and artificial intelligence tools to automate security processes.
What is artificial intelligence and machine learning?
In the context of information security, artificial intelligence (artificial intelligence, AI) is software that is able to interpret the state of the environment, recognize events occurring in it and independently take the necessary measures. AI is particularly good at recognizing patterns and anomalies, so it can be an excellent tool for detecting threats.
Machine learning systems are software that can independently learn from human-entered data and the results of actions performed. Means of machine learning are able to build predictions based on information about developments in the past.
The use of artificial intelligence and machine learning to detect threats:
Companies have already begun to use artificial intelligence and machine learning to recognize security threats and respond to them. Powerful tools have appeared, but you need to decide how to incorporate them into the overall cyber security strategy of the enterprise.
For example, at Barclays Africa, they use artificial intelligence to detect signs of system compromise on the local corporate network and in the cloud. It requires processing huge amounts of data, and due to the rapid change in the global landscape of threats and the growing interaction of attackers, they need the most advanced technologies and methods to counter.
By implementing machine learning, people can be assigned tasks that they can do better than machines. While complaining about the acute shortage of specialists, the bank notes that it is simply impossible today to solve security problems manually.
The use of artificial intelligence to ensure security is growing:
Artificial intelligence and machine learning greatly accelerate the response to threats, analysts recognize Nemertes Research. According to them, today it is already a serious market, formed under the influence of real need.
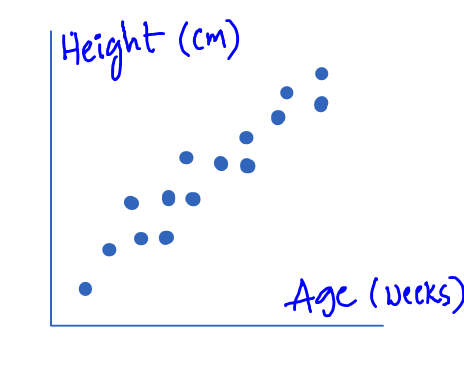
Nemertes conducted a global study on security, and its results show: on average, it takes 39 days to detect an attack and respond to it in organizations, but in some companies they managed to reduce this time to a matter of hours. The speed of response depends on the level of automation, which is provided by means of AI and machine learning.
The average attack detection time is an hour. In the most efficient machine learning companies, detection takes less than 10 minutes, and in lagging days it takes days or weeks. As for the average threat analysis time, it is three hours. In the best companies, such an analysis takes minutes, in the worst days or weeks. Behavioral threat analysis is already used in 21% of companies surveyed, and another 12% report that they will implement the appropriate funds by the end of this year.
At the forefront are financial services companies. Since their data is of increased value, they usually go one step ahead of everyone in cybersecurity and invest heavily in new technologies that are far from being cheap.
In terms of the scale of AI applications and machine learning in general, the figures are even higher. According to a Vanson Bourne study, today, 80% of organizations use artificial intelligence for certain purposes, and this is already paying off. It brings the most dividends in the field of research and development of new products – 50% of respondents reported that the innovation provides positive results. The second and third places are in the supply chain (46%) and core business (42%). Safety and risk management lagged behind: 40% of respondents reported positive experiences with AI in these areas.
These indicators will continue to grow: as revealed by a recent Spiceworks study, 30% of organizations with more than 1,000 employees use artificial intelligence in IT services, 25% are going to start doing this next year.
How artificial intelligence allows you to get ahead of intruders:
AI is improving as the amount of data received increases. With the accumulation of sufficiently large data slices, the systems are able to detect very early signs of the emergence of new threats. An example is SQL injection. The company Alert Logic quarterly collect data on approximately 500 thousand incidents occurring in 4 thousand of its customers. About half of these incidents involve SQL injection attacks. A single company in the world does not have the opportunity to consider each such incident separately, to find out if the injection attempt was successful, they are sure of Alert Logic.
Thanks to machine learning, the systems of the company not only process data faster, but also correlate events that occurred in different periods of time in different regions. Some attacks can be repeated in a few weeks or months, while starting from other parts of the Internet. If it were not for machine learning, such incidents at Alert Logic would have been missed, sure in the company.
Prospects for the use of artificial intelligence in the world of security:
Detecting suspicious user activity and network traffic is the most obvious use of machine learning. The current systems more successfully cope with identifying unusual events in large data streams, solving standard analysis tasks and sending notifications.
The next step is to use AI to deal with more complex problems. For example, the level of cyber risk for a company at any given moment depends on many factors, including the presence of patching systems, unprotected ports, the arrival of targeted phishing messages, the level of password reliability, the amount of unencrypted confidential data, and whether the organization is attacks from the security services of another state.